
Main points
- At the Kyiv International Cyber Resilience Forum 2026, white hat hackers tested the cybersecurity of an arms marketplace on the DOT-Chain Defence platform, using a specially created isolated environment.
- The winner of the competition was Bohdan Korzhynsky, who spoke about his work as a white hat hacker, emphasizing the importance of ethical testing and the advantages of Ukrainian specialists in this field.
- 1 Who are white hackers, what did they check and why?
- 2 Insider View: What are the advantages of Ukrainian hunters?
- 1 Who are white hackers, what did they check and why?
- 2 Insider View: What are the advantages of Ukrainian hunters?
Alongside cybercriminals who seek out vulnerabilities for profit or harm, so-called white hat hackers – professionals who test systems legally and with the owner’s consent – work. They use the same tools and methods, but with the opposite goal: to make digital infrastructure more resilient, not more vulnerable.
In a specially created testing environment as part of the Kyiv International Cyber Resilience Forum 2026, held in February, a team of white hat hackers tested the cybersecurity of the DOT-Chain Defence arms marketplace platform of the Defense Procurement Agency. It was a controlled format where participants worked in a separately deployed environment with test data and access to all functions. From the very beginning, the organizers emphasized the security of the process – so as not to break the working services, while at the same time seeing real weaknesses.
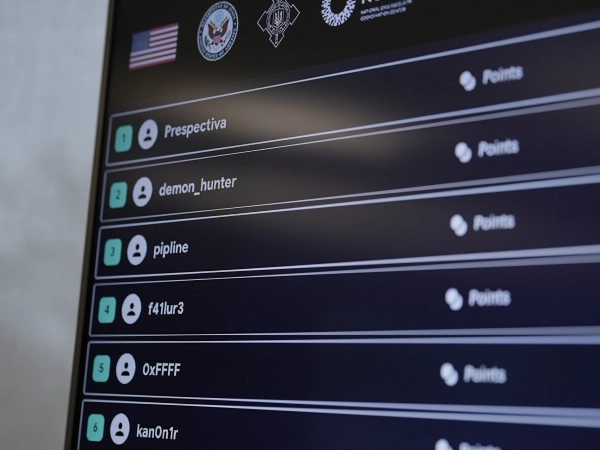
Testing took place within the framework of a special Bug Bash program – a format in which each vulnerability found is rated on a criticality scale, and the points are then converted into a share of the prize pool. According to one of the organizers, this allows balancing the motivation of participants and effectively distributing rewards among those who found the most significant flaws.
24 Channel spoke with the winner of the competition, Bohdan Korzhynsky , and tells us who “white hackers” are and what is the advantage of Ukrainians in this role.
Who are the white hackers, what did they check and why?
The event participants, who also call themselves “hunters,” worked in an isolated environment that mimicked a real production service.
Maksym Grabar , a representative of the DOT information security department, explains: the test environment is open only to specially approved testers, and in it they can work with all the functions of the service as if it were a real product. According to him, this makes it possible to simultaneously evaluate the logic, functionality and security of the services, without risking the leakage of real data.
White hacker teams / Photo provided by the organizers
The evaluation system worked on three levels: one point – average, three – high and five – critical. These points were summed up, and the prize fund was distributed proportionally to the results of each “hunter”. According to the organizer, the model involves several approaches to the budget: the first days there are some restrictions, and then those who continue work in different conditions, having the opportunity to work more deeply on more complex vulnerabilities.
In total, the system was tested by more than 20 participants, some of whom worked online. The organizers also emphasized that such specialists are checked by the relevant services to ensure that only ethical hackers participate in the testing – those who operate within the agreed scope and are ready for responsible disclosure.

Some of the participants / Photo provided by the organizers
The winners received certificates from the organizers on the main stage of the forum. Among them:
- first place, Bohdan Korzhynskyi – 300,000 hryvnias;
- second place, Vasyl Spachinsky – 125,000 hryvnias;
- third place, Ivan Slodzyk – 75,000 hryvnias.
Insider's view: what are the advantages of Ukrainian hunters?
Bohdan Korzhynskyi , who won the competition, told Channel 24 that his path to white hat hacking began with an interest in the inner logic of complex digital systems – not just the code, but also how they are designed and where they can fail. Over time, this became part of his professional activities.
My journey into the field of ethical hacking began with a classic technical interest in how complex digital systems work and where logical or architectural errors arise in them,
– he says.
According to Bohdan, testing is not a competition for the number of errors found:
For me, testing is not just “hunting for vulnerabilities”, but a tool for increasing the real resilience of Ukrainian digital systems.
He emphasizes that he chooses programs consciously – taking into account the social significance of the resource, the transparency of the rules and the clearly defined scope of testing, as well as the organization's willingness to promptly interact and fix problems.

Some of the participants / Photo provided by the organizers
Korzhynskyi notes that state resources are of particular importance, as they serve critical processes. He is currently participating in testing state resources of the State Enterprise Ministry of Defense “Defense Procurement Agency” and State Enterprise “Prozorro” as part of Bug Bash 2026, which was held during the Kyiv International Cyber Resilience Forum on the Bugstream platform. The format, he said, provided for clearly defined rules of interaction and a controlled process for finding vulnerabilities.
He also explains that technically the difference between ethical hackers and malicious hackers is minimal.
At the technology level, there is almost no difference. The same analysis methods, the same tools and approaches are used,
– he says.
At the same time, the key line runs in the legal plane and intentions: “An ethical hacker tests a system with the owner's consent to make it stronger, and reports the problem responsibly.”
Instead, a cybercriminal, according to a white hat hacker, looks for a way to exploit the vulnerability for gain or harm.
Korzhynsky emphasizes that transitions between these areas are possible: some specialists with deep technical knowledge consciously choose a legal format of work through bug bounty and bug bash programs, but there are also cases when the same competencies are used illegally.
I periodically participate in Ukrainian state initiatives, as well as global ones, in particular I have tested: IBM, Toyota, Ford, US Dept Of Defense, Yahoo, Shopify, OpenAI, Snapchat, Vimeo, Cloudflare, Starbucks, Xiaomi, General Motors, Malwarebytes, Samsung, Fortinet, Privatbank, Fuib, Palo Alto Software and other companies,
– Bogdan recounts.
He separately outlines the advantages of Ukrainian hunters, formed by working in conditions of constant cyberthreat. Among them:
- Practical experience in a complex environment – working with government, financial, and critical systems.
- Deep understanding of business logic – the ability to find not only technical but also logical vulnerabilities.
- Systems thinking – analysis not only through automated tools, but also through architecture and processes.
- High adaptability – quick response and effective work in conditions of increased intensity of cyber threats.
“Working in a high-intensity cyberthreat environment creates a different speed of thinking and responsibility,” he adds.
It is the combination of technical depth, practice, and systems analysis that makes Ukrainian specialists competitive in both state initiatives and international testing programs.