Main points
- NoVoice malware was discovered, infiltrating smartphones through more than 50 apps in the Google Play Store, which were downloaded 2.3 million times.
- The virus exploited Android vulnerabilities to gain root access, steal data, and remotely control devices.

The NoVoice virus has been spying on Android users for years / Collage by Channel 24/Freepik
Cybersecurity experts have uncovered a massive malware distribution campaign through Google's official app store, targeting millions of smartphone owners who had no idea their devices were being used by attackers.
What is NoVoice?
Cybersecurity researchers have identified a new malicious program called NoVoice. This virus was disguised as useful software in more than 50 applications placed directly on the official Google Play Store. According to available data, these applications managed to be downloaded more than 2.3 million times, which indicates the significant scale of the threat, writes PhoneArena.
The attackers used a proven tactic: they hid the virus “payload” inside programs that, at first glance, look completely safe and even useful. Among the infected software were utilities for cleaning the system from digital debris (cleaners), various games, and image galleries.
One specific example is the SwiftClean application from developer Biodun Popoola, which served as a carrier for NoVoice. The virus’s name itself comes from a specific cloaking technique: an audio file was found in the program’s code that was constantly playing at zero volume. This allowed the malicious code to run continuously in the background, remaining invisible to the user and built-in power saving features.
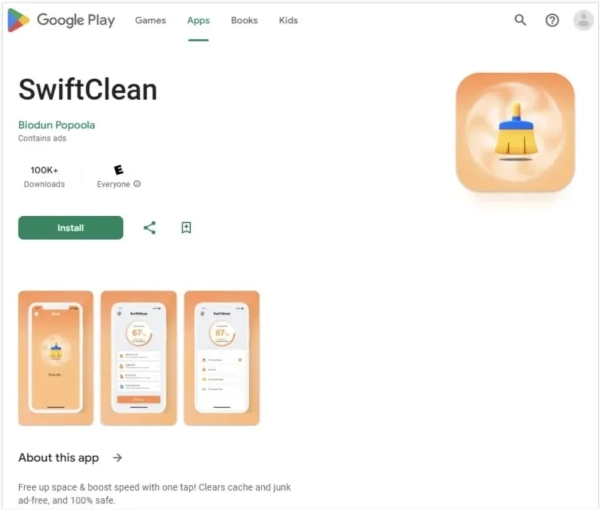
SwiftClean App / McAfee Screenshot
What does a virus do in the system?
The main danger of NoVoice lies in its ability to exploit vulnerabilities in the Android operating system to gain superuser rights, the so-called root access. Having obtained this level of control, hackers can not only steal confidential information, including logins and passwords to banking and financial services, but also remotely control the device, McAfee writes.
The virus can independently install new applications or delete existing ones without the knowledge of the smartphone owner. Moreover, in some cases, part of the malicious code penetrates so deeply into the system that even a complete reset to factory settings does not guarantee complete cleaning of the gadget.
Who is behind this?
An interesting detail of the study was the geographical aspect of the virus's operation. Experts noticed that NoVoice was programmed to not infect devices in certain regions, including Beijing and Shenzhen, writes Bleeping Computer.
Such selectivity usually indicates the origin of the attack developers: hackers try to avoid activity in their own country so as not to attract the attention of local law enforcement agencies.
What should users do?
Unfortunately, the report doesn’t provide a complete list of apps that were intentionally infected with the virus. However, there is good news: Google has already taken appropriate measures to protect users. The company said that its Google Play Protect service automatically removed dangerous apps from devices and blocked their reinstallation.
It also notes that smartphones that received security updates after May 2021 have built-in protection against this specific type of attack. For example, Pixel 6 models and newer devices that are regularly updated remain safe.
To minimize risks, experts recommend always downloading applications only from official sources and never ignoring system suggestions to install fresh security patches.