Main points
- Wikipedia was temporarily put into read-only mode due to an attack by a malicious Russian script that automatically edited pages.
- A malicious JavaScript worm modified 3,996 pages and corrupted the settings of 85 users, but the situation has been brought under control and data is being restored.
A dormant threat in the code: why Wikipedia suddenly banned editing its pages / Unsplash
The world's largest online encyclopedia has faced an unexpected technical challenge that forced its security team to temporarily suspend all editing of its content after it discovered malicious code capable of self-propagating and mass deletion of content.
What happened to Wikipedia?
The Wikimedia Foundation, a non-profit organization that oversees Wikipedia, was forced to urgently switch the resource to “read-only” mode. The decision was made after editors began to massively report strange activity: an unknown script was automatically editing pages, adding the text “We are closing the project” in Russian to the descriptions of changes, writes PC Mag.
As it turned out later, the cause of the incident was a JavaScript worm that has the ability to self-replicate within the system. The malicious code was not part of a targeted hacker attack that took place in real time. Instead, experts found that it was an old script called “test.js”, uploaded to the Russian-language segment of Wikipedia back in March 2024 by a user with the telling nickname “Ololoshka562”.
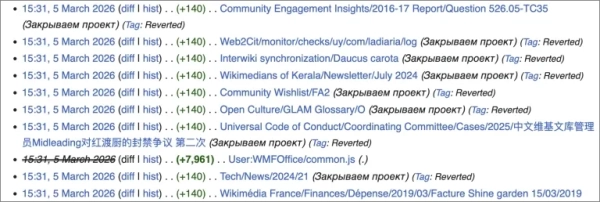
Edit history with Russian text / Photo meta.wikimedia.org
For almost two years, this file remained dormant until one of the Wikimedia Foundation employees accidentally activated it during a routine security check of user code.
The mechanism of action of this “worm” turned out to be quite dangerous for the integrity of the project. Once activated, it tried to intercept the sessions and privileges of administrators who were viewing infected pages. Having gained access to accounts with high rights, the script launched the “Special:Nuke” function – a special extension designed to allow moderators to quickly delete large amounts of recently created spam or vandalism. The program used this tool in endless loops, selecting random articles for destruction.
In addition to deleting content, the malicious code tried to ensure its survival in the system at two levels:
- First, he modified individual users' personal JavaScript files to run every time they accessed the site under their login.
- Secondly, if the victim had the appropriate rights, the worm attempted to make changes to the global file MediaWiki:Common.js, which is loaded for every visitor to the encyclopedia.
Thus, any administrator who simply opened the page to view could become an unwitting spreader of the virus.
According to Bleeping Computer, the malicious code remained active for only 23 minutes. During this short period of time, it managed to modify approximately 3,996 pages and corrupt the personal settings of 85 users.
The Meta-Wiki service, which hosts the foundation's documentation and projects, was the most affected. Some editors compared the incident to the actions of Russian groups of attackers who attacked wiki projects several years ago, indicating that the code likely originated from past vandalism campaigns.
Wikimedia Foundation representatives now assure that the situation is fully under control. All damaged or deleted data is being restored, and records of malicious edits have been hidden from the change history for the security of the platform.
The experts separately emphasized that no personal information of users was leaked. The account that became the source of the problem has been blocked, and the developers are working on new security tools that will help avoid accidental activation of outdated scripts in the future.